Thx. I’ll also check out the two writers you mentioned.
Dessalines
- 130 Posts
- 726 Comments
There’s a tendency for “soft-leftists” to co-opt already existing terms in the Marxist canon, de-fang them of any revolutionary rhetoric, repackage them, and market it to the masses. Mark Fisher, Zizek, Naomi Klein, are the major culprits.
Yes, the best book on this is Yasha Levine - Surveillance Valley . You can find the audiobook on torrents.
The purpose the the very first DoD networks, was as an anti-communist counter-insurgency tool, mainly to aid in the collection of data and the fight against communists in SE asia, particularly Vietnam.
I’ve found this also. He’s a liberal with zero class analysis or materialist literacy. If you’ve ever read his books, like his main one, enshittification, it reads like a middle-school age baby leftist wrote it.
It’s a testament to the sad state of US and canadian education that he’s considered a pioneer in any field.

 161·4 days ago
161·4 days agoObligatory US troop copypasta
You see american choppers in the bright blue sky, hundreds and hundreds of screaming american soldiers drop from it, you look across the field and see the tanks rolling in. You hear a loud explosion and realise that the shrine you have protected for thousands of years with tooth and nail is destroyed by the empire, you come to the realisation that this is very probably the end of your people who’ve struggled to survive all these centuries.You realise that very soon there is going to be a river of blood of your people here; white phosphorus and depleted uranium will be shot very soon, deforming babies for decades to come, and millions of your people are gonna be killed. Your millennia old language and religion will be wiped out, you’re very likely the last of your kind.
Suddenly, an American soldier kicks you down, puts his foot on your neck and aims his standard ar-15 on the side of your head all while screaming; you realise you’re gonna die, and you won’t have to see the destruction of your community that you fostered so carefully all these centuries for.
Just before he pulls the trigger, you think to yourself, “To be fair to him, he probably had a low GPA in highschool and didnt have a health-care, those are notoriously hard to get in America”.

 61·5 days ago
61·5 days agoYep I’ve found this too. DDG has more SEO / AI slop search results than nearly any other search engine.
Same. They seem great for local apps like keepass, but it could potentially be as dangerous as passwords if using a provider like google.
Too many people (i’d guess over 90% of internet users) don’t know about, or use password managers, so their default is to use the same easy to remember password for everything.
Also webauthn only lets the server see the public key, so servers can’t get away with storing unhashed passwords in their db.
Yes you can use your own password manager to store the passkeys. Like keepassxc on android. Then all your devices can use it.

 142·5 days ago
142·5 days agoDDG is almost all AI slop results now. Even worse than google.

 10·7 days ago
10·7 days agoWay too late for that. The best the democrats can muster is a former Abu Ghraib prison guard, who went back to Iraq several times to kill Iraqis, and was proud of it.

 18·9 days ago
18·9 days agoBots most likely. People creating many accounts on the more open signup servers, then running local bots that mass downvote certain users.
Downvote bots are IMO the current biggest spam vector on lemmy. Unlike posts / comments, its harder to detect that its a bot / AI doing it.
The next lemmy version will have the option to disable federated downvotes, which will make them all moot.

 19·9 days ago
19·9 days ago8 dead accounts were being used to follow and downvote your posts.

 5·17 days ago
5·17 days agoNice, seems really legit, especially since it works offline. Thx for that.
I’ve been trying to find a decent WYSIWYG android markdown editor (that’s not just a webview wrapper), but none exist yet. This should work in the time being.

 30·26 days ago
30·26 days agoSpain’s government only recently started turning against the US, and this vote was in 2022.
As for Ireland, can’t say.

 22·26 days ago
22·26 days agoBasically either the more honest, and less competent imperialists, vs the dishonest, more competent imperialists.

 37·26 days ago
37·26 days agoThe US and Israel were trying to push the women’s rights angle with their manufactured protests, then bombed a girls school killing ~150 mostly schoolchildren.

 4·26 days ago
4·26 days agoLove it, nice job!







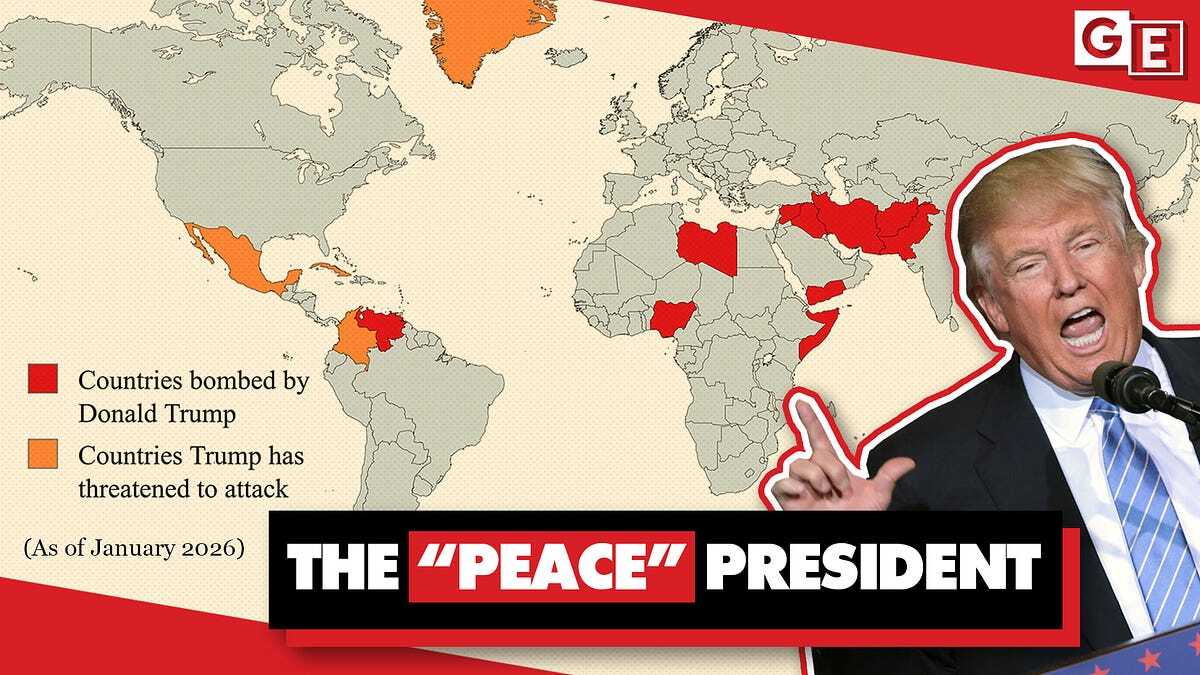





Pretty fitting that the US democrats main focus candidate right now is a former Abu Ghraib torture camp prison guard, who repeatedly says he signed up for the US military because he wanted to kill people.